Ransomware is a kind of malicious software, which stops user access to files in their systems. It encrypts files or the entire device and asks victims to pay a ransom to unlock their files or devices, or their files will be deleted permanently from their systems. All the infected file names will carry, .WCRY in the end.
The malware can enter into computers via several ways like spam emails, phishing attacks and malicious downloads from the web. Since its launch, ransomware has become a popular method for hackers to extract money from companies and consumers.
Ransomware infections are not new. They had already harassed enterprises, small business owners and individuals since mid of the 2000s. Internet Crime Complaint Center (IC3) reported more than 7,600 attacks between 2005 and March 2016.
With their capability to encrypt files on the hard drive, Cryptolockers have become the biggest threat computer users are facing during recent years. Users are asked to pay hundreds or thousands of dollars to regain access to their data.
What is WannCry Ransomware attack?
This is not the first time ransomware infected computers, but the recent WannaCry Ransomware attack on Friday 12 May 2017, is documented as the largest cyber-attack in the history. This malicious software infected more than 230,000 computers in over 150 countries.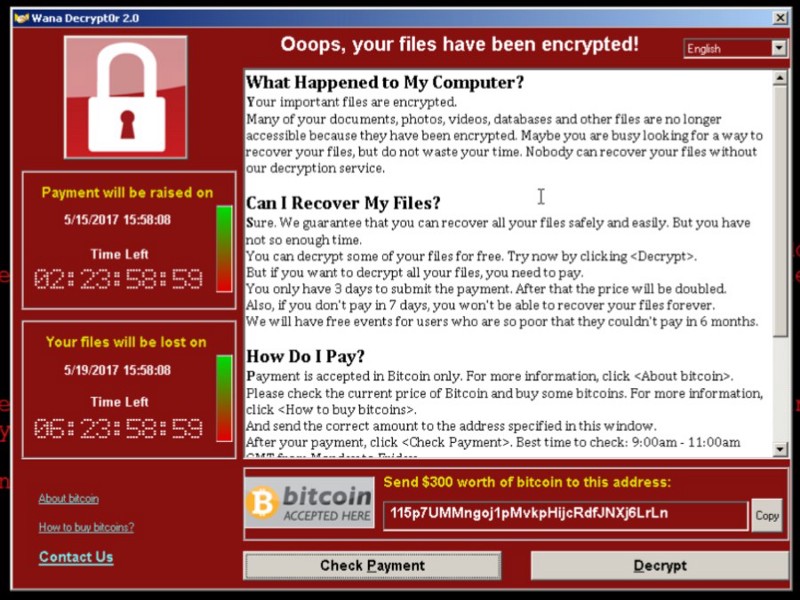
The outbreak globally affected the countries and companies along with Parts of Britain’s National Health Services, Spain's Telefónica, FedEx and Deutsche Bahn. Xinhua, a news agency in China reported that around 30,000 of computers had been hit while Japanese computer experts stated the total number of 2,000 PCs had been affected by this viral attack.
The recent outbreak demands users to pay the ransom of $300 (£230) in Bitcoin after locking their computer systems. According to Bitcoin wallet analysis, £33,000 in ransoms were paid.
How does it work?
WannaCry Ransomware cryptoworm targets computers running the Microsoft Windows operating system and older unsupported versions of Microsoft Windows like Windows XP, Windows Server 2003 and Windows 7.
A person who receives this malware code on their computer either via email, network or web download, this virus attack system hard drive and started encrypting files. After encrypting the data, it notifies the person to send the mentioned payment in Bitcoin if they want their data back.
The latest Ransomware, is found to be extremely dreadful due to its capability to spread automatically throughout the network after a single download. It uses file sharing ports in the network and infects all the devices on the network.
This malware was actually spread via suspicious emails, telling users that their computers are exposed to the bug regardless of all the care and prevention. The only way to protect computers from ransomware is to run a security patch and secure their data backup.
What should victims do immediately after ransomware message?
Although it happens very quickly, if a user is lucky enough to realize in first few seconds that he has received a malware, he should power off his system immediately. After that, he must proceed to boot the device via external disk and run cleaning tools like Nortorn Power Eraser. This might stop ransomware to encrypt all the files.
However, Nortorn Internet Security and Power Eraser tools can efficiently clean the virus from the machine, they can’t unlock the encrypted files in the system. The best way to restore computers is to use data backup or reset factory settings with a recovery disk, which is followed by immediate update and application of all security patches.
What are the best practices to protect against ransomware attack?
Both enterprises and individual users can significantly reduce the risk of becoming a victim of malware outbreaks after following few fundamental practices of cyber security. These practices include regular software updates, backing up data and avoid downloading and opening suspicious links from web and email.
Software updates include not only updating operating systems and applications, but also include security patches and antiviruses. Never turn off auto-update option.
Beware of email attachments that require enabling macros to view the content. Unless a user is not sure about the sender, such emails must be deleted immediately.
Its user responsibility to back up all important data to restore files, once the infection has been cleaned up.
Storing data on cloud servers can also reduce the severity of ransomware attacks, as these servers usually maintain encrypted versions of files that can be un-encrypted to restore data files.
How to recover data after Ransomware attack?
Security researchers have discovered software tools to unlock encrypted data after ransom malware attacks. WannaKey and WannaKiwi are two data recovery software that is capable of recovering prime numbers required to encrypt data from affected computer memory. If the ransom code is found, this software recreates the encryption key to decrypt data. However, this software can recover data from devices that are not rebooted yet.
In addition to these data recovery software, security researchers and developers also created Kill Switch to stop spreading the malware attack in the network. This was discovered after registering the domain name found in the code of ransomware.
Bottom line:
Although security researchers are working to develop data recovery tools to decode encrypted files in the user system, organizations and individual users must follow the standard security measures to protect their computer machines from viral and ransomware outbreaks.
Auhtor Bio: 
Daniel Smith is a web developer who works at Logo Glaze, a custom logo design company. In his leisure time, he loves to write blogs and articles related to his field as sharing information helps build awareness in readers and that’s his only goal.
 Table of Content
Table of Content